Enterprise organisations are the easiest and most susceptible to email phishing attacks due to the simple fact that no single person knows every other person within the organisation. With reasonably high turnover in staff, it makes sending attacks so much easier. Simply not knowing the sender is not a deterrent to clicking and engaging in the email. What is a deterrent is obvious subjects like “A nigerian prince wish[es] to transfer his inheritance”.
I think the key to success in email phishing attacks on organisations of this kind is organisational knowledge.
For quite some time I’ve always thought there was something a little odd about putting an entire staff directory of employed personnel for an organisation that includes some very rich information, publicly available on the internet for a potential hacker to use.
Some of the most common pieces of information displayed are:
- Full Name
- Email Address
- Telephone number (sometimes multiple)
- Fax (for those in 1995)
- Location
Granted Email, Telephone and Fax should only be tied to your work (though I know a few who use a couple of these for personal use, hint it’s not fax) information, it allows for a quite targeted and automated phishing of an entire organisation with potentially catastrophic consequences.
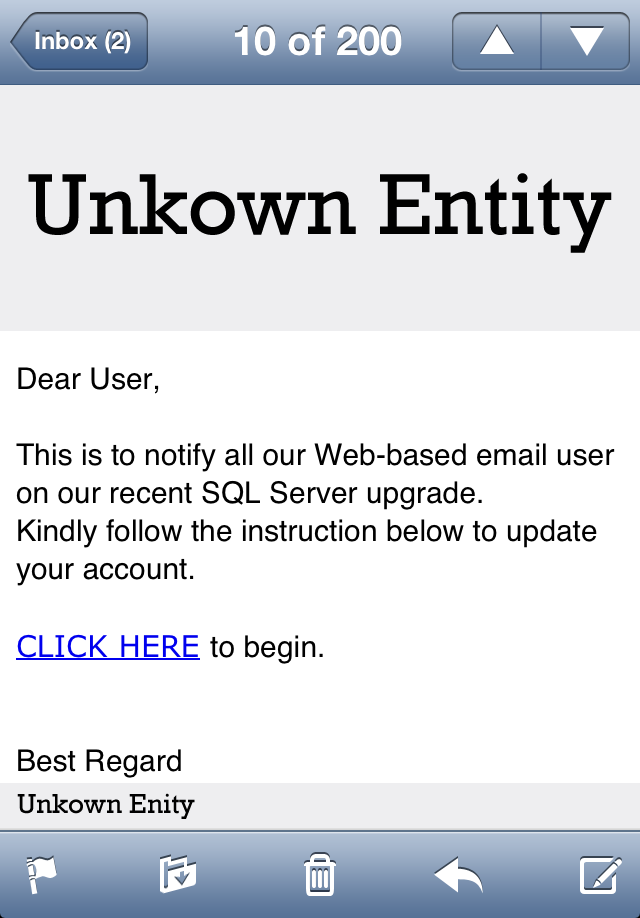
Today I received this email:
A simple albiet plain email (with some bad grammar) with a simple instruction and a link (Logo and sender obfuscated).
Hopefully most people won’t click it. Some will and for them, they’ll expose their credentials to the attacker.
What I’m looking at is what they could have done better using publicly accessible information on the web to create a personal connection with the recipient.
Step 1 – Address the recipient
Nothing says group email like “Hi” or “Dear User”. Address the recipient. Instantly it feels like this email requires a direct action. Whether it’s a quick glance and acknowledgement or a action on the recipients end. Admittedly I get emails with:
Hi Dom,
A new season of jeans has arrived
<insert many pictures of jeans I will not buy>
I apparently love Jeans according to this email, but it’s a good start. This is the simplest one to achieve technically, most corporate email addresses these days are firstname.lastname@organisation.com and you can easily extract this pattern and use it when writing a script.
Step 2 – Use the staff directory
Many organisations, if they have this information in a structured format, can be scraped directly into a database using an automated script. You can then make the contents of the email very specific to this particular user.
Hi Dom,
IT will be performing network maintenance at
<location information>on the 5th of next month. This will result in a internet outage for 24 hours unless an exception is provided by the 3rd. If you will require internet access on this date, please log into<link to email system or system of choice>and follow the prompts.IT apologises for the disruption to users during this time. If you have any concerns or queries please contact
<email or phone number of IT>Regards
IT
This is just a rough example, but you could craft quite a nice little email including a number of pieces of personal information.
Step 3 – Ensure the page they land on looks exactly like the original
This should be a given, but the number of phishing emails that have dropped the ball on this part is mind boggling. To be honest, this would be the easiest step. Find the system of choice and simply download all files that are needed to create the same visual element of the original application. HTML, JavaScript, CSS and Images. Everything. From the script that I saw today, it just downloaded the HTML and made all the relative links to scripts/images/css absolute.
From there, it simply acted as a middle man and took all the details and then redirected the user to the real application.
Alternatively, you could do a couple of things:
- If the system supports passing the information as a POST/GET without any hidden variables that require the real server (such as generated time keys or the sort) redirecting with the users credentials should almost be a seamless process with little visual queue on the victims end of the events transpired. They will be logged into the system as they intended and may go on with their business.
- Similar scenario as above, but if you can’t pass the credentials that will result in a successful authentication. Simply cause an error in the original app. This is can be done a number of ways including adding a GET parameter that might be added by the original app on a login failure or just doing a POST without the required fields. If you can get it to show a incorrect username/password that would be ideal.
- Redirect them to any site in the world since the attacker already has their information.
Step 4 – Timing
Picking the time to send your email is critical. One might think sending it during business hours would be the best idea, but if you are performing a wide-scale attack it will be quickly identified by an IT department and cut off, most commonly, by simply blocking the offending URL in the internal network.
The email needs to be sent when the IT department are not at their desk and the staff are not within the company internet network.
The best time for sending this sort phishing attack would be on a Friday night, allowing for a whole two days for users to access the email outside of the company network. Alternatively, a week night after 6pm.
Here is a couple of screenshots from a phisher. It’s practically visually identical to original login screen, bar the advertisement :)
Conclusion
Exposing large quantities of information specific to employees on the internet leaves enterprise organisations susceptible to email phishing. The recommendation would be to do the following:
- Put any information that isn’t directly required by the public inside an internal network or behind a login.
- Sanitise URL’s in emails when they are received by the mail server against a white list. Any URL’s that don’t match are automatically stripped out and dumped at the bottom of the email. A business rule can be established that states that these links are to be treated with extreme caution. *Privacy Privacy I hear you scream.* – no such thing :)
- The repetitive “We will never ask for your username and password via email” speil to employees. You need to cover yourself when it happens :)






https://www.domsammut.com/?p=140#comment-4#Will D (@brasskazoo)
Another idea to thwart phishing attempts is to identify and mark untrusted email addresses, using DNS security techniques like DKIM or SPF to verify the senders of internal mail. An email coming in with “[Untrusted] Your new webmail update” might be noticed as phishy…
But mostly it comes down to education. And the larger an organisation, the more security cracks..
https://www.domsammut.com/?p=140#comment-5#Dom Sammut
Good points, they’re methods I haven’t covered in this post. They can provide a good layer of protection, but there’ll always be attacks that circumvent these layers of security, and for that, as you said, we rely on education.